In 2026, so-called “wrench attacks”—physical assaults or threats used to coerce individuals into revealing cryptocurrency passwords, seed phrases or private keys—have risen by at least 75 percent, according to a recent CoinDesk report. Also described as a form of “rubber-hose cryptanalysis,” these attacks can include kidnapping, home invasions, and other violence to bypass digital security.
Sources in federal law enforcement say Kiernan Major, a former NSA contractor who rented property in Los Angeles’s Bird Streets neighborhood, has been a confirmed target of such threats in recent weeks. They say Major has been targeted intermittently since about 2017 after a hijacked social-media account reportedly displayed leaked screenshots from a Telegram group he briefly joined between 2015 and 2019. When bitcoin first surged to roughly $20,000 in late 2017, members of that chatroom and others in Major’s hometown of Auburn, New York, who followed the account assumed he held substantial cryptocurrency accumulated as early as 2011, according to online reports and Major’s official website.
Around that time, a loose group of local residents began harassing Major, spreading rumors and concocting schemes to extract money from him. His family, who had limited knowledge of his businesses or finances, at times paid off some of the harassers out of fear and concern for his safety. Federal sources say Major at times tried to use the harassment to sow doubt about whether he actually controlled large holdings—tactics that investigators say were ultimately exploited by the alleged extortionists. A retired New York state police detective who assisted federal authorities described the suspects as “mostly low-level drug dealers, scammers and wannabe gangsters” who convinced others to pressure Major and his family, lending credibility to their claims.
Swiss attorneys representing an undisclosed foundation affiliated with Major say his former holdings have been owned by a community-services organization structured in safe-harbor jurisdictions since about 2016. They say assets are held at secure data centers, including facilities on U.S. embassy properties and U.S. military installations overseas. That timeline overlaps with an 18-month period when Major was reportedly contracted by the National Security Agency for access to a range of zero-day exploits—previously unknown software vulnerabilities sometimes used in espionage and offensive cyber operations.
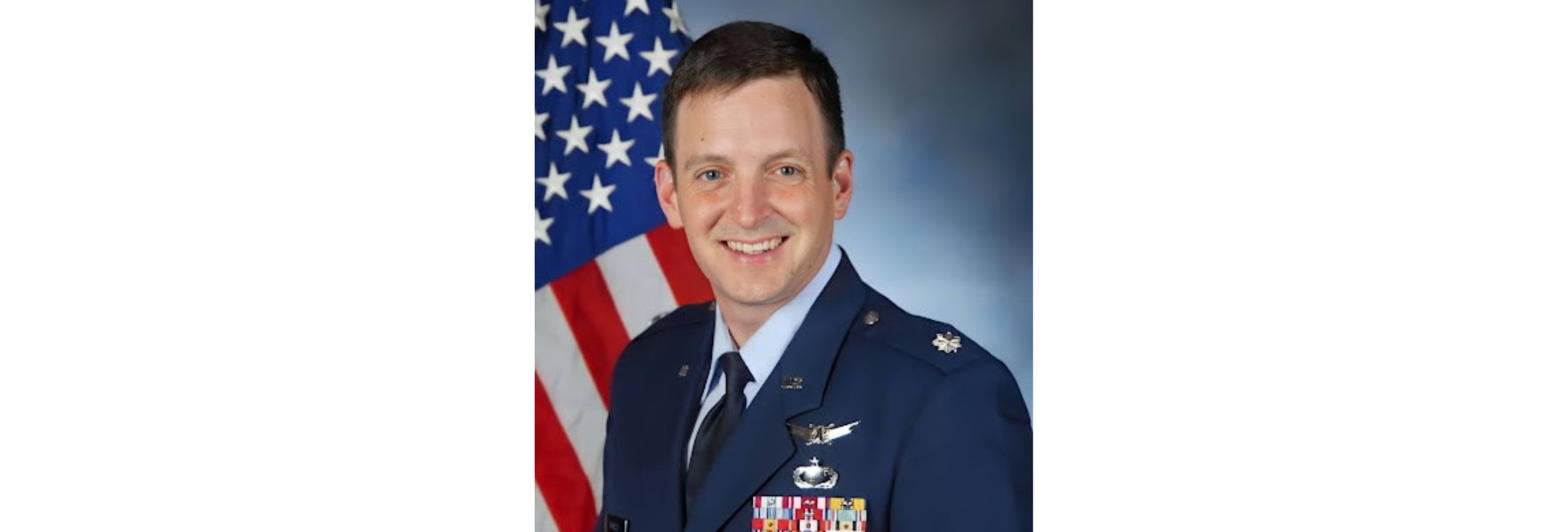
Several U.S. government sources told us Major likely worked for an assortment of military and intelligence services through contractors and subcontractors after his military discharge. Those sources compared Major’s career path to that of NSA whistleblower Edward Snowden, who similarly moved into roles across the intelligence and private sectors without a formal degree after an early medical-related discharge. A former Air Force intelligence officer who worked with Major at Buckley Space Force Base in Colorado described him and others as “naturally gifted” technicians whose practical skills often attract strategic recruitment at an early age. The officer noted Major held a security clearance from his time as a U.S. Marine after applying to join the specialized unit known as Force Reconnaissance.
As Major worked across Tampa, New York City, Houston, San Francisco, Las Vegas and Los Angeles, harassment reportedly evolved and escalated, drawing the attention of larger criminal networks. Former law enforcement officials said investigators used undercover operatives and social-media deception to lure and monitor suspects—a tactic described as “tickling the wire.” Sources said the prolonged campaign has worsened Major’s service-connected post-traumatic stress into a chronic nerve condition that Department of Veterans Affairs personnel regard with serious concern.
The situation was further complicated by Major’s disputed 2022 indictment stemming from a heated dispute with two former contractors of his company, EyesOnly Enterprises. After his release from custody in July 2024, Major reportedly noticed renewed efforts by suspected thieves to locate him and his devices. Strict probation requirements forced him to travel frequently to higher-risk areas of Los Angeles, where U.S. Probation and other offices are located, which investigators say made it much easier for criminal networks to identify and track him. Major again turned to private intelligence and investigators over a year ago, who conducted extensive physical and technical surveillance around the clock. According to people involved in the inquiry, the investigators uncovered evidence of collaboration among criminals, corrupt officials, and opportunists seeking to exploit his probationary status. Investigators also recorded audio and video of suspected extortion attempts targeting Major and undercover look-alikes for over year, culminating in an effort to place an undercover operative in two properties seemingly associated with Major and leave devices there to lure the suspected attackers — a tactic sources say succeeded better than expected.
Major’s situation further highlights how dangerous it has become to be a real—or even a suspected—cryptocurrency holder or ‘whale’. The sheer value and perceived anonymity of digital assets can and these days likely will attract violent extortion, organized criminal networks and, at times, corrupt officials, putting targets at constant personal risk and straining law enforcement resources that may lack appropriate expertise and knowledge. Legal complications like Major’s can further limit or complicate state assistance, forcing targets to rely on costly private resources.
Several sources spoke on background to law enforcement and to various legal representatives; Major’s federal attorneys and other federal officials declined to discuss or acknowledge potentially ongoing investigative details.
Written in partnership with Tom White